What is Data Security? Definition, Examples, and Best Practices
With an increase in data usage comes an increased responsibility to protect this data and the privacy of the individuals it represents. But what exactly is data security, how do you measure its effectiveness, and what are some best practices for ensuring it? In this article, we'll dive into the nuts and bolts of data security as it relates to data analytics.

Imagine a security breach exposing critical data, like customer credentials or financial information. The results would be catastrophic: loss of customer trust, heavy regulatory fines, and even potential employee churn as they seek companies with better customer data management processes.
What is Data Security & Privacy?
Put simply, data security is the practice of protecting data against unauthorized access, use, theft, or destruction. It encompasses a wide range of technologies, processes, and policies designed to safeguard data from potential threats. Data privacy, on the other hand, deals specifically with protecting personal information from intrusive or harmful use. It includes regulations such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA).
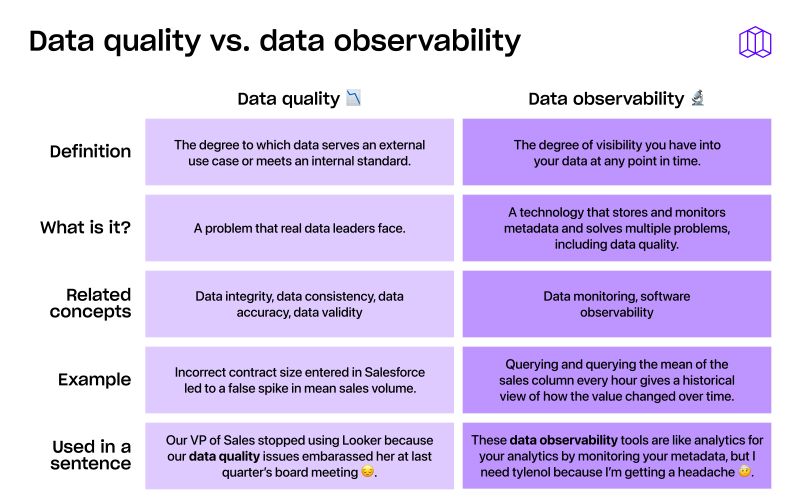
Data security is one of ten dimensions of data quality. Other dimensions include completeness, accuracy, consistency, validity, and reliability. Ensuring data security is important because insecure data can lead to a damaged reputation, loss of revenue or customers, regulatory fines, and litigation. The protection of data against unauthorized access is also known as data privacy.
Examples of Insecure Data
Now that we know what data security is and why it's important, let's take a look at some examples of insecure data and their negative impacts on business analytics.

- Exposure of sensitive data: If you're the Head of Data at Wordle Industries, an international conglomerate expanding Wordle into international markets with 3 and 4 letters, you might have an activated_users table that your marketing team uses to send marketing emails. If this table gets exposed, it could lead to the exposure of sensitive user data, including email addresses and other personally identifiable information.
- Manipulation of data: If an employee tries to manipulate data intentionally, it can lead to errors in decision-making. For example, someone might change a value in the daily_revenue table to make it look like the company is hitting its targets, when in fact, it's not.
- Loss of data: Finally, if your organization experiences a data breach or sudden outage, it can lead to the loss of data. Imagine losing your daily_revenue table, which contains valuable data that your VP of Sales needs to make decisions. In such cases, your organization may face reputational damage, financial loss, and other negative consequences.
How do you Measure Data Security?
Now that we know some examples of insecure data, we need a way to measure data security. Here are a few metrics that teams use to measure data security:
Data encryption coverage: Encryption is the process of converting data into a code that only authorized users can read. Measuring the percentage of encrypted data can give you a rough estimate of how secure your data is.
User authentication attempts: User authentication is the process of verifying that a user is who they say they are. This is typically done with a combination of usernames, passwords, and multi-factor authentication. Measuring failed authentication attempts and successful logins can give you an idea of how secure your user authentication process is.
Time to breach detection: In the unfortunate event of a data breach, time to detection is the time between when the breach occurred and when it was detected. This metric is important because the longer it takes to detect a breach, the more damage can be done.
How to Ensure Data Security
Now, let's take a look at some best practices for ensuring data security.
- Access control: Access control is a crucial aspect of data security and should be implemented across the entire data ecosystem. It involves limiting who can access data, which data they can access, and for what purpose. This means that the access granted should be based on business needs and job functions.
- Regular backups: Data backups ensure that you have a copy of your data, and they're critical in case of data loss, disasters, or system failures. You should consider using automated backups, so your data is copied frequently, and you don't have to worry about manually doing it.
Summary
In conclusion, data security is the practice of protecting data against unauthorized access, use, theft, or destruction. Insecure data can lead to damage to a company's reputation, loss of revenue, regulatory fines, and litigation. Data observability enhances data security initiatives by providing real-time visibility into data operations, enabling proactive identification of potential vulnerabilities, threats, and breaches. Metaplane is a data observability platform that enables data teams to maintain data quality through monitoring and troubleshooting tools. Its user-friendly design is tailored to the modern data stack and provides data observability business benefits to companies relying on data analytics and data warehouses.
Table of contents
Tags
...
...